Computer hacking is hacking into a computer system to obtain sensitive information, data, or control systems. People often commit cybercrime or do it for personal enjoyment.
Hackers can hack computers because of weak security. Most computer systems today are vulnerable to hacking due to vulnerabilities in the system’s design, coding, and configuration. Teams of hackers have developed various hacking techniques to gain access to sensitive information stored on a computer system. Hackers can use such information in many ways for their benefit.
Most hackers use hacking techniques to commit cyber crimes such as phishing fraud, internet threats, identity theft, and data mining.
Cyber terrorists or criminals who aim to cause monetary losses and damage an organization’s reputation also go by the name of these criminals. Here are 11 Effective methods to hack a computer.

11 Effective Ways To Hack Computers
Computer hacking is the process of accessing and exploiting vulnerabilities in electronic systems. It involves hacking into a computer system to obtain unauthorized access to the system or cause damage. Various methods, including phishing, social engineering, and malware attacks, carry out hacks.
Phishing is a fraudulent internet activity in which someone persuades someone to provide personal information via email or a fake website.
In social engineering, hackers use fake websites or other means to get people to reveal their personal information, such as passwords. Malware attacks involve using malicious software on a computer system without the user’s knowledge or consent.
These methods can lead to serious consequences, including financial losses, identity theft, and loss of critical data. Therefore everyone must be aware of the potential dangers of hacking and take steps to prevent it.
1. Use Spyware And Malware.

There are a variety of hacking methods that can be used to hack into a computer system. However, one of the most common ways hackers hack into computers is through spyware and malware. Spyware is a type of malware that secretly gathers data from the user’s Computer. It can be used for various purposes, including gathering information about the user’s online activity and stealing confidential data.
Malware is another type of software that harms the victim’s computer system by damaging it, stealing information, or disabling security features.
In addition to installing antivirus software on your computer and keeping it up-to-date with security patches, there are several effective ways to protect yourself from spyware and malware attacks. One method is to only download software from trusted sources and avoid clicking on links from unknown sources.
2. Teal Data

Teal data is malicious software that enables cyber criminals to steal sensitive information from infected computers. And Teal data can be spread through email attachments, infected websites, or malicious software installed on the victim’s Computer.
Once installed, teal data can automatically perform various malicious tasks, such as stealing passwords and banking information, slowing down system performance, or destroying data.
Attackers can use teal data to launch attacks on other computers in the network. There are several effective ways to hack computers using teal data.
For example, users can use anti-malware programs to protect their computers from infection and update software regularly to ensure security vulnerabilities are patched. Additionally, users can create strong passwords and take other basic steps to protect their systems from hackers.
By taking these steps, users can keep their personal and financial information safe from hackers and ensure the security of their computers.
3. C Cess Confidential Information

There are various ways to hack computers, and each method has unique benefits and drawbacks. One common way to hack computers involves accessing confidential information or crashing the system. However, hacking computers without leaving any traces can be challenging.
Some effective methods for hacking computers without leaving any evidence include developing custom software or applications.
That can be used to access confidential information or perform other tasks on the system. As well as using password recovery tools and changing passwords frequently. If you are looking to hack computers but need help with the technical aspects, there are many online resources that can help you do this.
4. B Tain Password And Login Information
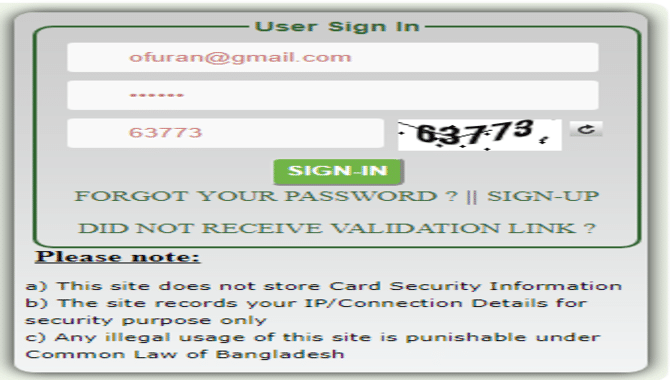
Password hacking is a common practice for hackers. They often target users who use the same password for multiple accounts or use weak credentials such as easy-to-guess passwords or simple passwords.
It is common for hackers to exploit security vulnerabilities in websites or applications to gain access to users’ accounts.
Users can protect themselves from malicious attacks and stay safe online by knowing how hackers hack computers. It is important to have a unique password for every account, use different passwords for different accounts, and ensure that those passwords are secure and not easily guessed.
5. Ontrol Computer Operations
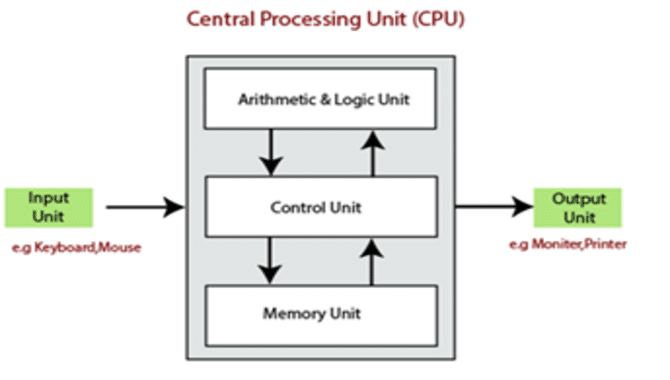
There are various ways to hack into a computer system, and each method has advantages and disadvantages. One effective way to hack into a computer is through malware.
Users can unknowingly install malware on their computers. Once installed, it can take over the computer’s operating system and perform malicious tasks without the user’s consent.
Various methods can remove malware from a system. But it is often difficult to do so without affecting the performance of the Computer. Another effective hacking strategy is phishing attacks. In phishing attacks, Email messages that appear to come from trusted sources trick users into revealing their personal information. Such as work colleagues or organizations that they regularly interact with online.
By using social engineering techniques, hackers can help create believable email messages that appear to be legitimate requests for account credentials or other confidential information. To protect against hacking attacks, users should always use strong passwords and monitor their online activity closely.
6. Ack Into An Email And Social Media Accounts

There are a number of effective methods you can use to hack into email and social media accounts. One common technique is called “brute force,” which involves trying every possible password combination until you find the right one.
Another method is called “spear phishing,” which involves sending fake emails or social media messages with links that attempt to steal your login information. Scareware uses fake warnings about viruses or other threats to scare you into giving away your login information.
By hacking into email and social media accounts, you can easily access sensitive information such as bank accounts, passwords, and other personal information. If you want to keep your online accounts secure from hackers, use strong passwords, update security software, and avoid clicking on suspicious links or attachments in email messages.
7. Anipulate Web Traffic
There are many effective ways to hack computers, but password hacking and malware installation are the most common methods. Hackers commonly manipulate web traffic.
This involves manipulating the traffic on a website by injecting malicious code into web pages or hijacking the user’s browser. Other hacker techniques include appending code to web pages or overloading a website’s servers with requests.
Hackers can use these methods to steal personal information or inject ads into web pages. Other hacker techniques can be very powerful, but they are only effective if you know how to use them properly.
8. Infiltrate Networks
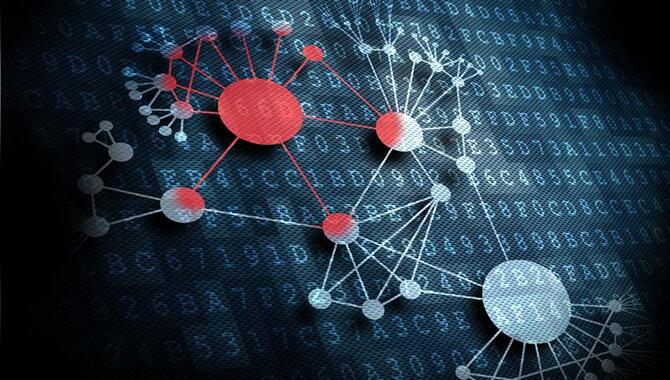
N filtrate networks is a powerful computer security software that allows users to hack into other computers. This software can be used to access sensitive information and steal passwords from other devices. It also allows users to install malware, which can be used to perform a range of malicious activities on a target computer.
N filtrate networks are available as a paid subscription or a free trial, allowing users to test the software and decide whether it is right for their needs. If you want access to other networked devices, N filtrate networks are a must-have hacking tool.
9. Bypassing Login Password On Macos
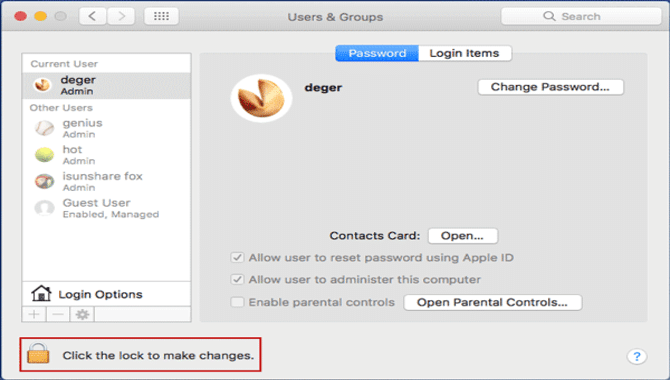
There are a variety of methods you can use to bypass login passwords on macOS. Whether using a password reset tool or a third-party password manager, you can easily gain access to accounts without knowing the actual password.
After accessing the user’s account, you can perform various tasks, such as deleting files or accessing sensitive information.
However, hacking and stealing data is risky, and users must exercise caution and protect their online accounts. You should be aware of the risks involved in hacking and take steps to protect yourself and your data.
10. Bypassing Login Password On Windows
Attackers can easily bypass Windows login passwords if they know the user’s name and password. Windows, by default, stores login passwords in plain text format, which makes them vulnerable to hacking attacks. This can allow unauthorized users to access the user’s Computer.
To protect yourself from this type of attack, use a strong and unique password for each of your online accounts. Using a password manager, such as LastPass or 1Password, can help you generate unique passwords for each online account, making it harder for hackers to guess your login password.
Using a password manager, you can automatically generate unique passwords for all your online accounts without having to remember different passwords. This will make it more difficult for hackers to access your account if they know your username and/or email address.
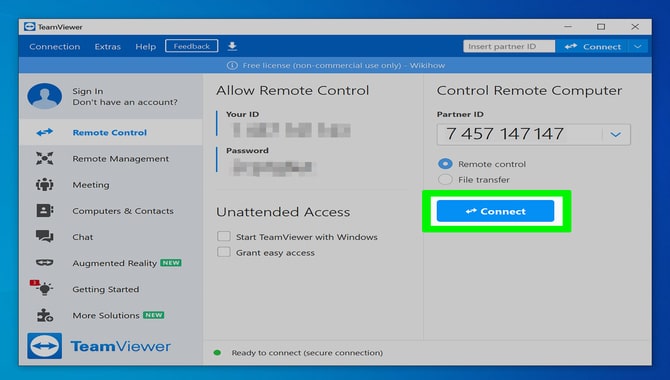
11. Remotely Hacking Via Team viewer

Team Viewer is a software that enables users to connect to other computers over the internet. People can use it for various purposes, such as remote assistance, diagnostic purposes, and more. However, Hackers have used this software to hack systems and steal sensitive data.
Therefore, This software should only be used in cases of emergency, and users must be aware of the risks involved. It is important to ensure that only reliable sources of assistance use TeamViewer and adhere to its terms and conditions.
How To Prevent Computer Hacking?

It is possible to prevent computer hacking by following a few simple steps. The first and foremost thing is to install a firewall on your Computer. This will help protect it from unauthorized access.
Another important step is to use antivirus software. This can help keep your computer malware free and ensure it remains secure. Using a password manager, you can create strong passwords for all your online accounts and protect them with a password manager.
You should also keep your Computer up-to-date with the latest security patches and software updates. These can help protect your device from vulnerabilities and other issues. Besides, two-factor authentication can further protect your account from unauthorized access.
Finally, you should avoid clicking on links in unsolicited emails or downloading any attachments without verifying the source. Besides, you should encrypt your data and use a VPN if possible.
Is Computer Hacking Illegal?
Although people may consider computer hacking a criminal offense, it is not illegal. Some governments have enacted legislation to prevent and punish computer hacking.
Hackers can use many methods to hack a computer. Hackers may access personal data, passwords, and email addresses using viruses, Trojans, and other malicious software.
They may also cause a financial loss by accessing sensitive information stored on a company’s server or stealing payment information from a user’s online account.
Hacking can cause serious financial losses and damage to businesses. Therefore, Businesses need to secure their servers properly and ensure that users’ login credentials are secure.
Conclusion
Teens should be aware of recent advances in computer hacking to minimize its risks and prevent it from happening in their home or school environment. They should also be cautious about internet scams involving hackers using social engineering tactics to steal personal information from users.
It is advised to use strong passwords and utilize two-factor authentication when possible. Ensure that your operating system and software are up-to-date, and keep your Computer protected with a solid internet security solution such as one from McAfee.
If you want to hack computers, we recommend utilizing social engineering as an alternative. In addition, password management tools such as password managers can help safeguard your password security.
Frequently Asked Questions:
1.Is It Possible To Hack The Computer System?
Ans: Yes, it is possible to hack a computer system. Hackers can access your computer system through various methods, such as viruses and malware. They can steal information or compromise the security of your system. Protecting your computer system by installing updated software and security measures is important.
2.How Do People Hack Computers?
Ans: Computer hacking can be divided into two main categories: active and passive.
Active hacking involves attacking a system in order to gain access to it or steal data. Passive hacking involves spying on or monitoring a system without engaging in any active attacks.
Some common methods used by hackers to hack computers include installing malware, cracking passwords, and exploiting vulnerabilities.
3.What Do Most Hackers Use To Hack?
Ans: Most hackers use various software applications and tools to hack into a computer. These tools can include viruses, worms, and Trojan horses. Viruses are small programs that attach to email or other file types and then spread to other computers when opened or forwarded.
Worms are digital insects that travel through networks like the internet and degrade system performance or destroy data. Trojan horses have disguised programs that allow hackers to access systems without the user’s knowledge or consent.
4.What Software Do Hackers Use To Hack?
Ans: Hackers use different software applications to hack into computers and steal data. These applications can include malware, ransomware, and viruses.
Malware is hacking software used to break into a computer and steal data or confidential information. Malware can be spread through email, social media, or websites.
5.How Can I Minimize The Chances Of Being Hacked On My Computer?
Ans: There are a few ways to protect your Computer from being hacked.
- Use a firewall and antivirus software:
- Keep your Computer up-to-date with the latest security patches:
- Use strong passwords:
- Do not click on links in unsolicited emails:

Leave a Reply